Introduction
Whenever security professionals recommend the 5 most important IT security practices to average users, one of the items is usually something like: "Avoid using open Wifi" or "Always use VPN while using open WiFi" or "Avoid sensitive websites (e.g. online banking) while using open WiFI", etc.
What I think about this? It is bullshit. But let's not jump to the conclusions. Let's analyze all risks and factors here.
During the following analysis, I made two assumptions. The first one is that we are comparing public WiFi hotspots with no encryption at all (referred to as Open), and we compare this to public WiFi hotspots with WPA2-PSK (and just hope WEP died years before). The other assumption is there are people who are security-aware, and those who just don't care. They just want to browse the web, access Facebook, write e-mails, etc.
The risks
Let's discuss the different threats people face using public hotspots, compared to home/work internet usage:
1. Where the website session data is not protected with SSL/TLS (and the cookie is not protected with secure flag), attackers on the same hotspot can obtain the session data and use it in session/login credentials stealing. Typical protocols affected:
- HTTP sites
- HTTPS sites but unsecured cookie
- FTP without encryption
- IMAP/SMTP/POP3 without SSL/TLS or STARTTLS
2. Attackers can inject extra data into the HTTP traffic, which can be used for exploits, or social engineer attacks (e.g. update Flash player with our malware) – see the Dark Hotel campaign
3. Attackers can use tools like SSLStrip to keep the user's traffic on clear text HTTP and steal password/session data/personal information
4. Attackers can monitor and track user activity
5. Attackers can directly attack the user's machine (e.g. SMB service)
WPA2-PSK security
So, why is a public WPA2-PSK WiFi safer than an open WiFi? Spoiler alert: it is not!
In a generic public WPA2-PSK scenario, all users share the same password. And guess what, the whole traffic can be decrypted with the following information: SSID + shared password + information from the 4-way handshake. https://wiki.wireshark.org/HowToDecrypt802.11
If you want to see it in action, here is a nice tutorial for you
 |
| Decrypted WPA2-PSK traffic |
Any user having access to the same WPA2-PSK network knows this information. So they can instantly decrypt your traffic. Or the attackers can just set up an access point with the same SSID, same password, and stronger signal. And now, the attacker can instantly launch active man-in-the-middle attacks. It is a common belief (even among ITSEC experts) that WPA2-PSK is not vulnerable to this attack. I am not sure why this vulnerability was left in the protocol, if you have the answer, let me know. Edit (2015-08-03): I think the key message here is that without server authentication (e.g. via PKI), it is not possible to solve this.
Let me link here one of my previous posts here with a great skiddie tool:
To sum up, attackers on a WPA2-PSK network can:
- Decrypt all HTTP/FTP/IMAP/SMTP/POP3 passwords or other sensitive information
- Can launch active attacks like SSLStrip, or modify HTTP traffic to include exploit/social engineer attacks
- Can monitor/track user activity
The only difference between open and WPA2-PSK networks is that an open network can be hacked with an attacker of the skill level of 1 from 10, while the WPA2-PSK network needs and an attacker with a skill level of 1.5. That is the difference.
The real solutions
1. Website owners, service providers should deploy proper (trusted) SSL/TLS infrastructure, protect session cookies, etc. Whenever a user (or security professional) notices a problem with the quality of the service (e.g. missing SSL/TLS), the service provider has to be notified. If no change is made, it is recommended to drop the service provider and choose a more secure one. Users have to use HTTPS Everywhere plugin.
2. Protect the device against exploits by patching the software on it, use a secure browser (Chrome, IE11 + enhanced protection), disable unnecessary plugins (Java, Flash, Silverlight), or at least use it via click-to-play. Also, the use of exploit mitigations tools (EMET, HitmanPro Alert, Malwarebytes AntiExploit) and a good internet security suite is a good idea.
4. Don't click blindly on fake downloads (like fake Flash Player updates)
5. The benefits of a VPN is usually overestimated. A VPN provider is just another provider, like the hotspot provider, or the ISP. They can do the same malicious stuff (traffic injecting, traffic monitoring, user tracking). Especially when people use free VPNs. And "Average Joe" will choose a free VPN. Also, VPN connections tend to be disconnected, and almost none of the VPN providers provide fail secure VPNs. Also, for the price of a good VPN service you can buy a good data plan and use 4G/3G instead of low-quality public hotspots. But besides this, on mobile OSes (Android, iOS, etc.) I strongly recommend the use of VPN, because it is not practically feasible to know for users which app is using SSL/TLS and which is not.
6. Use a location-aware firewall, and whenever the network is not trusted, set it to a Public.
7. In a small-business/home environment, buy a WiFi router with guest WiFi access possibility, where the different passwords can be set to guest networks than used for the other.
Asking the question "Are you using open WiFi?", or "Do you do online banking on open WiFi?" are the wrong questions. The good questions are:
- Do you trust the operator(s) of the network you are using?
- Are the clients separated?
- If clients are not separated, is it possible that there are people with malicious intent on the network?
- Are you security-aware, and are you following the rules previously mentioned? If you do follow these rules, those will protect you on whatever network you are.
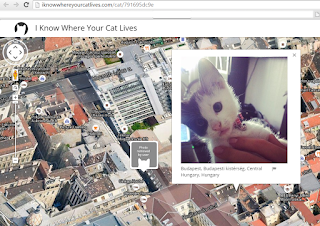
And call me an idiot, but I do online banking, e-shopping, and all the other sensitive stuff while I'm using open WiFi. And whenever I order pizza from an HTTP website, attackers can learn my address. Which is already in the phone book, on Facebook, and in every photo metadata I took with my smartphone about my cat and uploaded to the Internet (http://iknowwhereyourcatlives.com/).
Most articles and research publications are full of FUD about what people can learn from others. Maybe they are just outdated, maybe they are not. But it is totally safe to use Gmail on an open WiFi, no one will be able to read my e-mails.
PS: I know "Average Joe" won't find my blog post, won't start to read it, won't understand half I wrote. But even if they do, they won't patch their browser plugins, pay for a VPN, or check the session cookie. So they are doomed to fail. That's life. Deal with it.
Related word
- Nsa Hack Tools
- Hacker Tools 2019
- Pentest Tools Review
- Hack Tools Download
- Tools For Hacker
- Best Hacking Tools 2019
- Pentest Reporting Tools
- Pentest Tools Github
- Tools Used For Hacking
- Pentest Tools Github
- Pentest Tools Github
- Hackrf Tools
- Pentest Tools Website Vulnerability
- Usb Pentest Tools
- Hacker Tools
- Pentest Tools For Ubuntu
- Hacker Tools For Windows
- Physical Pentest Tools
- Hacking Tools Name
- Pentest Tools Framework
- Hack Tools Mac
- Hacker Tools Software
- Hacker Tools Free
- Tools 4 Hack
- Hack And Tools
- Hacking Tools For Mac
- Pentest Tools For Windows
- Hacking Tools
- Hack Tools
- Hacker Tools Free Download
- Easy Hack Tools
- What Are Hacking Tools
- Blackhat Hacker Tools
- Hack Tools 2019
- How To Hack
- What Are Hacking Tools
- Underground Hacker Sites
- New Hack Tools
- Pentest Reporting Tools
- Pentest Tools Open Source
- Hacking Tools Windows
- What Is Hacking Tools
- Termux Hacking Tools 2019
- Hacking Tools Name
- Hacking Tools Kit
- Hacking Tools Kit
- Hacking App
- Hacker Tools Free Download
- Hacking Tools Windows
- Hacking Tools 2020
- Hackrf Tools
- Pentest Tools Website
- Hacking Tools For Windows
- Hacking Tools And Software
- Hack Tools For Windows
- Hacking App
- Hacker Security Tools
- Pentest Tools Nmap
- Hacker Tools Apk
- Hacker Tools For Windows
- Hacking Tools 2019
- Easy Hack Tools
- Hacks And Tools
- Wifi Hacker Tools For Windows
- Hacking Tools For Games
- Pentest Tools Kali Linux
- Hacker Tools Windows
- Tools 4 Hack
- Hacking Tools Mac
- Hack Tools
- Hacking Tools Usb
- Pentest Tools
- Hacker Tools List
- Tools 4 Hack
- Hacking Tools For Kali Linux
- Tools 4 Hack
- Hacker Tools For Pc
- Pentest Tools Website
- Hacking Tools Online
- Hacking Apps
- Beginner Hacker Tools
- Pentest Tools Website
- Hacking Tools Pc
- Pentest Tools Alternative
- Hacking Tools 2020
- Pentest Tools Windows
- Hacker Tools
- Hack Website Online Tool
- Game Hacking
- Pentest Tools Website
- Hack Tools
- Hacking Tools Kit
- Hacking Tools Online
- What Is Hacking Tools
- Pentest Tools Windows
- Hack Tools 2019
- Hack And Tools
- Hack And Tools
- Hacking Tools Kit
- Pentest Tools Website Vulnerability
- Hacker Tools For Ios
- Blackhat Hacker Tools
- How To Hack
- Pentest Box Tools Download
- Hack Tools
- Hacking Tools And Software
- Pentest Tools Online
- Pentest Tools Bluekeep
- Hack Tools For Windows
- Best Hacking Tools 2019
- Best Hacking Tools 2019
- Hack Tools Download




ليست هناك تعليقات:
إرسال تعليق